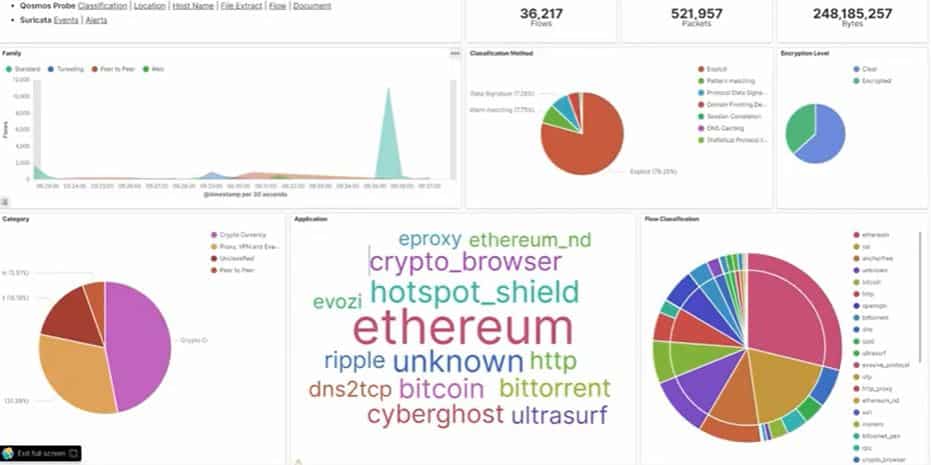
Industry-Leading DPI and IP Traffic Classification
Enea Qosmos’ Deep Packet Inspection (DPI) and classification technology identifies data traveling over networks in real time, providing a true picture of the traffic by identifying protocols and types of applications, and extracting additional information in the form of metadata.
Enea’s market leading next-generation DPI engine, Qosmos ixEngine®, recognizes over 4500 protocols and applications – more than any other on the market. Solution vendors in networking, cybersecurity, and telecommunications use the technology to gain application visibility, accelerate time to market and benefit from continuous signature updates.
Accurate, Comprehensive Classification of Network Traffic
Enea Qosmos technology typically recognizes over 97% of network traffic including regional applications. Each signature is augmented with specific characteristics (such as family and tags) to enhance service awareness and enable highly accurate processing. These advanced techniques also mean that our technology can classify most types of encrypted traffic.
Enea Qosmos DPI and Traffic Classification: Key Capabilities
- Full support for more than 4500 protocol signatures, without counting specific workflows and application variants.
- Identification of service types within applications, e.g. chat, video, voice, file transfer.
- Recognition rate of fully encrypted protocols based on new statistical algorithms with self-learning capabilities. Applications like Vuze®, uTorrent®, BitTorrent® are correctly identified 95% of the time.
- Custom Signature Module to create customized signatures for any category of application including URLs, HTTP based applications, binary applications, etc.

Machine Learning and Encrypted Traffic Classification
Enea is committed to protecting data privacy while ensuring solution vendors retain the essential traffic visibility required to manage and secure networks. This visibility challenge mounts daily as the use of encryption expands, and more stringent standards like TLS 1.3 emerge.
Integrating Enea Qosmos technology helps vendors successfully meet this challenge. The Enea Qosmos Encrypted Traffic Classification (ETC) toolkit includes advanced analytical techniques combined with machine learning (ML) that enable solutions to identify applications, categorize traffic, and extract valuable metadata from encrypted traffic. Specific techniques that are paired with ML include statistical and behavioral analysis, DNS-based classification and the use of the first packet processing with advanced multi-tiered caching, with methods often combined for best results.
Detection of Anomalous and Evasive Traffic
Vendors also rely on Enea Qosmos technology to help meet the challenge of detecting advanced threats. Enea Qosmos ixEngine supports this effort by producing valuable security-related traffic classification and computed metadata. This includes identification of evasive techniques like complex tunneling, file spoofing, domain fronting, and the use of covert communication channels, unauthorized VPNs, anonymizers, and more. It can also identify anomalous traffic and specific threats, such as potential MITM attacks or the presence of cryptocurrencies and mining pools. It can further extract critical data for analysis by security components, such as embedded links in emails.
Continuous Protocol and Application Updates
Enea has more than 15 years of expertise in identifying IP protocols and applications and detecting their changes. This enables us to remain one step ahead of the competition and offer the most complete and reliable Next Generation DPI and classification engine.
Our international team of protocol experts and developers work continuously to gather traffic samples and reverse engineer new protocols. Our long experience ensures a solid software supply chain based on robust processes and in-house tools, such as the Protocol Development Language (PDL) and protocol signatures in data format. These processes and tools speed protocol plugin development and make our technology more accurate while ensuring the highest standards of quality.
We can also provide the tools for customers who want to develop specific signatures themselves.
DATASHEET
Enea Qosmos ixEngine: Next-Generation DPI Engine for Maximum Traffic Visibility

Enea’s next-generation DPI engine, Qosmos ixEngine, identifies over 4500 applications and protocols, more than any other on the market.