Real-Time DPI-based Application Awareness for Cybersecurity Solutions
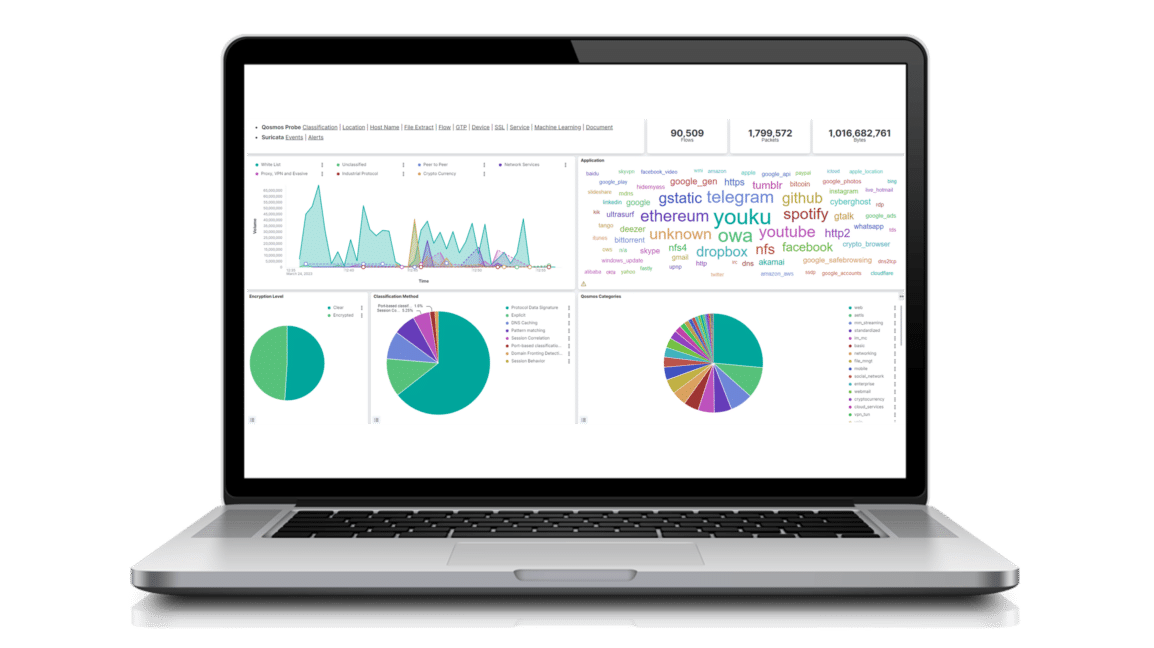
Enea provides network traffic visibility and application awareness to vendors of cybersecurity solutions through its embedded next-generation Deep Packet Inspection (NG DPI) products, the Enea Qosmos ixEngine and Enea Qosmos Probe.
These products enhance solutions with real-time information on traffic flows including applications, services, content, users, and transactions. They also enable the identification and classification of encrypted and evasive traffic.
Enea also offers IDS-based threat detection capabilities as an SDK. Enabling easy and tight integration with cybersecurity solutions, the Enea Qosmos Threat Detection SDK has the potential to double performance while remaining highly flexible and scalable.
Enea’s DPI-based Network Traffic Visibility for Cybersecurity Vendors
2023 INDUSTRY REPORT
Artificial Intelligence in Cybersecurity
Enea’s next-generation DPI engine, Qosmos ixEngine, identifies over 4500 applications and protocols, more than any other on the market.
Latest Resources and Industry Insights
Industry Recognition



DATASHEET
Enea Qosmos ixEngine: Next-Generation DPI Engine for Maximum Traffic Visibility

DATASHEET
Enea Qosmos Probe: A Network Traffic Sensor with Next Generation DPI